With the rise of supply chain attacks, the security of suppliers, clients and business partners is under increased scrutiny.
This led security rating provider SecurityScorecard and the Cyentia Institute to investigate organizations' worldwide vendor risk exposure in a new study called Close Encounters of the Third (and Fourth) Party Kind, published on February 1, 2023.
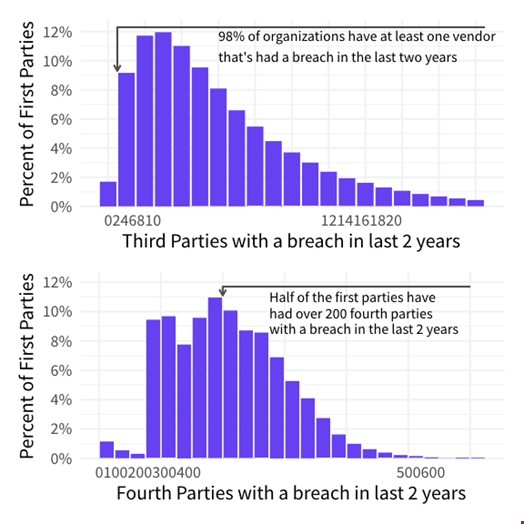
They found that 98.3% of organizations worldwide work closely with at least one third-party vendor that has been breached in the last two years and that over 50% of them have an indirect relationship with 200 fourth-party vendors – third-party vendor’s partners or suppliers – that have been breached in the last two years.
“A data breach is one of the most obvious and serious symptoms of a security issue,” Mike Woodward, Vice President of Data Analytics at SecurityScorecard, told Infosecurity.
“That’s why these staggering numbers are very concerning,” he said.
Degrees of Separation
This high degree of exposure to supply chain breaches comes from various factors, the report states.
First, organizations rely on a high number of third and fourth parties. On average, a business maintains a relationship with 10 third-party vendors – 15.5 in the healthcare sector and 25 in the information services industry.
Then, for every third-party vendor in their supply chain, organizations typically have indirect relationships with 60 to 90 times that number of fourth-party relationships.
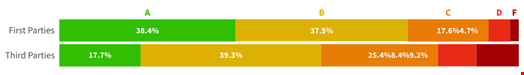
The report also shows that third-party vendors fare significantly lower in terms of security than primary organizations. For instance, twice the proportion of primary organizations achieves the highest security rating of A, while third parties are nearly five times more likely to receive an F on their scorecard, according to SecurityScorecard’s rating system.
Moreover, researchers found that organizations with poor security posture and lower security scores have twice the number of third-party vendors and 10 times the number of fourth parties, thus multiplying the risks.
“An organization’s attack surface spans beyond just the technology that they own or control,” Aleksandr Yampolskiy, SecurityScorecard’s CEO, said in a statement.
This has been shown multiple times, including in the 2018 British Airways hack, Woodward added. “It came through the Swissport vendor. When British Airways told the Information Commissioner’s Office (ICO) in the UK that the breach targeted its vendor, the ICO responded that it was British Airways’ responsibility, and that the airline was getting fined anyway.”
Visibility and Patching Policy
To reduce their exposure to these risks, Woodward said organizations should be more aware of what they and their partners have installed and whether it is updated regularly and patched when needed. “It departments could also insist that the employee update their systems regularly, through implementing a security policy within the company and across its supply chain.”
“We see hints from some regulators that they are going to start mandating this kind of programs, Woodward added.
“Organizations need visibility into the security ratings of their entire third and fourth-party ecosystem so that they can know in an instant whether an organization deserves their trust and can take proactive steps to mitigate risk,” Yampolskiy said.
This resonates with Joe Biden’s 2021 Executive Order on Improving the Nation's Cybersecurity, which introduces the idea of requiring US organizations to produce software bills of materials (SBOMs), an up-to-date list of all products– hardware and software – used across all services as well as their versions and their potential unpatched vulnerabilities.
SecurityScorecard’s report was based on data analysis from over 235,000 global, primary organizations and more than 73,000 vendor products.
