Chinese state-sponsored actor APT40 is focusing on exploiting newly discovered software vulnerabilities (N-days), often within hours of public release, a joint government advisory has warned.
The Australian Signals Directorate’s Australian Cyber Security Centre (ASD’s ACSC), alongside agency partners from the US, UK, Canada, New Zealand, Germany, South Korea and Japan, noted that the group prefers to exploit vulnerable, public-facing infrastructure over techniques that require user interaction such as phishing campaigns.
APT40 conducts regular reconnaissance against target networks to identify vulnerable, end-of-life or no longer maintained devices on networks of interest, and to rapidly deploy exploits.
It is capable of exploiting newly public vulnerabilities in widely used software such as Log4j, Atlassian Confluence and Microsoft Exchange within days or even hours of public release.
“Notably, APT40 possesses the capability to rapidly transform and adapt exploit proof-of-concept(s) (POCs) of new vulnerabilities and immediately utilize them against target networks possessing the infrastructure of the associated vulnerability,” the advisory read.
Read here: Vulnerability Exploitation on the Rise as Attackers Ditch Phishing
The group continues to find success exploiting vulnerabilities from as early as 2017.
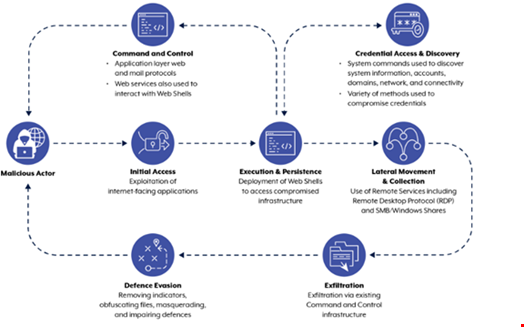
Once inside a network, APT40 specializes on evasion and persistence techniques to exfiltrate sensitive data on behalf of the People’s Republic of China (PRC) Ministry of State Security, the agencies assessed.
APT40 has repeatedly targeted Australian networks as well as government and private sector networks in the region, and remain a threat to the other authoring agencies’ nations.
The group’s activity and techniques overlaps with threat actors tacked as Kryptonite Panda, GINGHAM TYPHOON, Leviathan and Bronze Mohawk in industry reporting.
How APT40 Conducts Operations
The ASD said that APT40 has embraced a global trend of using compromised devices, including small-office/home-office (SOHO), as operational infrastructure last-hop redirectors for its operations in Australia.
Many of these SOHO devices are end-of-life or unpatched, offering a soft target for N-day exploitation. Once compromised, such devices also provide a launching point for attacks to blend in with legitimate traffic, obfuscating malicious activity.
This technique is also regularly being used by other PRC state-sponsored actors, the authoring agencies said.
This approach represents an evolution in APT40’s tradecraft, with the group previously using compromised Australian websites as command and control (C2) hosts for its operations.
The advisory also provided case studies of past APT40 attacks, which highlighted tactics, techniques and procedures used by the group to move laterally through networks while avoiding detection post compromise.
These case studies highlighted the following common themes:
- Host enumeration, to build a map of the target network
- Exploitation of internet-facing applications and web shell use to gain an initial foothold on the network and ability to execute commands
- Exploitation of software vulnerabilities to escalate privileges
- Credential collection to enable lateral movement
Security Recommendations for APT40 Target Organizations
The agencies issued a series of recommendations to mitigate the techniques employed by APT40. These include:
- Ensure security patches or mitigations are applied to all new vulnerabilities in internet exposed devices and services within 48 hours
- Where possible, use the latest versions of software and operating systems
- Segment networks to limit or block lateral movement by denying traffic between computers unless required
- Disable unused or unnecessary network services, ports and protocols
- Use well-tuned Web application firewalls (WAFs) to protect web servers and applications
- Enforce least privilege to limit access to servers, file shares, and other resources
- Use multi-factor authentication (MFA) and managed service accounts to make credentials harder to crack and reuse
- Retain comprehensive historical logging information across areas like web server request logs, Windows event logs and internet proxy logs to enhance the effectiveness and speed of investigations
- Replace end-of-life equipment
- Review custom applications for functionality that can be misused and reduce, remove or disable where possible
