In the first half of 2024, the number of reported Common Vulnerabilities and Exposures (CVEs) has increased by 30% compared to last year, totaling 22,254. However, just 0.91% of reported CVEs were weaponized, according to Qualys.
This figure, highlighted in Qualys’ 2024 Midyear Threat Landscape Review, underscores the increasing complexity of the cybersecurity landscape and the growing need for enhanced protection measures.
The report, published today, suggests that this significant rise in vulnerabilities is driven by the advancing complexity of software and the pervasive use of technology, necessitating more dynamic and advanced vulnerability management strategies.
The review emphasizes the critical threat posed by the weaponization of vulnerabilities. Although only 0.91% (204 vulnerabilities) of the reported CVEs have been weaponized, these represent the most severe risks, frequently exploited through ransomware and other malware by threat actors.
Notably, there’s been a 10% increase in the weaponization of older CVEs in 2024, indicating a persistent danger from previously identified vulnerabilities.
According to the report, public-facing applications and remote services are the primary targets for initial access and lateral movement within networks. Exploiting these vectors allows attackers to infiltrate systems and move laterally, posing significant security risks. For example, CVE-2023-43208, which impacts healthcare systems, illustrates how vulnerabilities in critical sectors can have widespread and severe consequences.
Read more on tackling these threats: How to Build Cyber Resilience in Healthcare
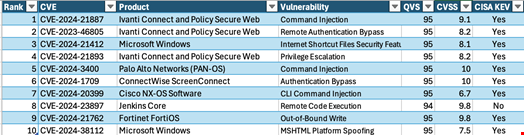
Ransomware continues to be a prominent threat, according to the report, with six major vulnerabilities linked to ransomware campaigns. Additionally, three out of ten of the most exploited vulnerabilities in the last year were from Ivanti.
The Qualys findings underscore the necessity of leveraging and integrating threat intelligence with vulnerability management tools. By prioritizing actively exploited vulnerabilities and conducting regular scans, companies can enhance their security posture.
“Organizations must ensure regular updates, diligent patch management, and advanced threat detection systems are in place to mitigate the risks associated with high-critical vulnerabilities,” the company wrote.
“We strongly recommend that organizations conduct risk assessments and adopt a comprehensive approach to vulnerability management. Prioritize addressing vulnerabilities actively exploited in the wild (such as CISA KEV), those with a high likelihood of exploitation and those for which weaponized exploit code is available.”
