Lazarus Group has been observed continuing its VMConnect campaign by targeting developers with new malicious software packages on open source repositories, according to ReversingLabs.
The researchers said that the North Korean group posed as employees of major financial services firm Capital One, using fake job interviews to lure developers into downloading the malware.
The malware is designed to install malicious downloaders on developer systems capable of fetching second and third stage malware, such as backdoors and infostealers.
Attackers Masquerading as Capital One
The attackers impersonated staff at US financial services company Capital One to send developers “test” packages through links in LinkedIn direct messages in the recently observed campaign.
These links took the targets to the GitHub repository as a “homework task.”
The files in the repository purported to be coding skills tests linked to job interviews. For example, the researchers observed archives with names like Python_Skill_Assessment.zip and Python_Skill_Test.zip.
The archives contained a README file with instructions for the developer, with a timeframe set for completing the assignment.
“It is clearly intended to create a sense of urgency for the would-be job seeker, thus making it more likely that he or she would execute the package without performing any type of security or even source code review first. That ensures the malicious actors behind this campaign that the embedded malware would be executed on the developer’s system,” the researchers said.
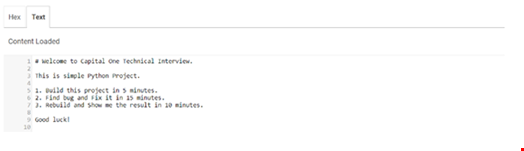
The content of the README files included with the packages contained instructions for the job candidates to find and fix a bug in a password manager application, republishing their fix and taking screenshots to document their coding work.
Link to Previous VMConnect Campaigns
The fresh activity is believed to be linked to the VMConnect campaign that was first identified in August 2023. The initial campaign was discovered on the Python Package Index (PyPI) open-source repository and involved the continuous posting of new malicious PyPI packages daily.
In September 2023, ReversingLabs uncovered three additional malevolent Python packages that are believed to be part of this extended campaign: tablediter, request-plus and requestspro.
The campaign was linked to the notorious Lazarus Group following research conducted by Japanese CERT.
ReversingLabs also encountered malware hidden in compiled Python files in the latest activity observed.
The malware code identified in the new campaign was contained in altered pyperclip and pyrebase modules. The code was implemented as a Base64 encoded string which hides downloader code. The malicious functionality in this file was identical to that observed in the samples from earlier iterations of the VMConnect campaign.
The researchers observed other similar behaviors with the new set of packages, including the targeting of Python developers in addition to npm and Javascript, posing as financial services firms and the use of fake job interviews to lure targets.
Lazarus Campaign an Active Threat
While this activity dates back more than six months, ReversingLabs said there is evidence that the Lazarus Group’s VMConnect campaign is an active threat. For example, on July 31, the researchers found a newly published GitHub repository named “testing” that was nearly identical to the earlier GitHub archives and contained the same malicious code.
“Since the entire campaign has been active since early 2023 and new malicious samples and projects still surface from time to time, we believe it is safe to call this an “active campaign” and one that will likely remain active for some time,” the firm wrote.
The researchers noted that the use of open source packages and platforms to target developers are a growing trend among sophisticated cybercriminal and nation-state groups.
Organizations are advised to be vigilant against such downloads and ensure developers and other technical staff are educated on the dangers of downloading and executing code from an unknown source on their system.
