The LockBit ransomware strain continues to be the primary digital extortion threat to all regions, and almost all industries globally, according to a report by ZeroFox.
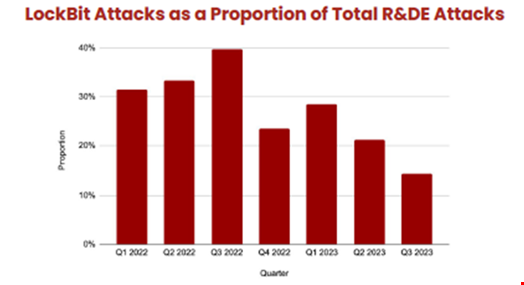
Researchers found that LockBit was leveraged in more than a quarter of global ransomware and digital extortion (R&DE) attacks in the seven quarters analyzed from January 2022 to September 2023.
This includes 30% of all R&DE attacks in Europe and 25% in North America during the period.
However, ZeroFox said that the overall proportion of attacks that LockBit accounts for is on a downward trajectory. This is likely due to increasing diversification of the R&DE landscape, with ransomware-as-a-service (RaaS) offerings lowering the barriers to entry for threat actors.
LockBit Trends in North America
The researchers noted that historically LockBit has been consistently under-deployed in attacks against North America compared to other regions, such as Europe. An average of 40% of LockBit victims were based in North America, but there is evidence this is on an upward trajectory, expected to reach 50% by the end of 2023.
The industries most frequently targeted by LockBit in North America between January 2022 and September 2023 were manufacturing, construction, retail, legal & consulting and healthcare.
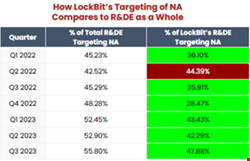
Meanwhile, LockBit made up 43.41% of R&DE attacks in Europe in Q1 2022, but decreased to 28.48% in the final quarter of the period, Q3 2023.
LockBit Intrusion Vectors
Due to the wide range of LockBit operators, a variety of intrusion methods have been used to deploy the payload.
The primary techniques identified were:
- Exploiting Internet-Facing Applications. These were primarily a range of remote code execution and privilege escalation vulnerabilities.
- Phishing. LockBit affiliates leveraged a variety of phishing lures to access victims’ networks, including attaching malicious documents and fraudulent resume and copyright-related emails.
- External Remote Services. Threat actors leverage legitimate user credentials obtained via credential harvesting to access external-facing remote working services.
- Drive-by Compromise. Operators have been observed accessing systems via a user visiting a website, often targeting the user’s web browser to do so.
- Valid Accounts. Threat actors frequently compromise credentials to bypass access controls, establish persistence, escalate privileges, and evade detection.
While the proportion of R&DE attacks LockBit accounts for is falling, ZeroFox said it expects the strain to remain one of the greatest threats “against almost all industries in all locations.”
The cybersecurity firm also noted that LockBit affiliates are shifting their focus towards organizations they believe are more likely to pay ransomware demands, such as professional services, education and financial sector organizations.
The Rise of LockBit
The LockBit ransomware strain was first identified in September 2019 and is run as RaaS offering. It is popular with a range of threat actors due to its speed of compromise and worm-like capabilities that enable self-propagation across a compromised network.
The strain is believed to be behind a number of recent high profile ransomware attacks this year, including Royal Mail, Boeing, and the Industrial and Commercial Bank of China (ICBC)
A report by Acronis in June 2023 found that LockBit was the most active ransomware strain in terms of total number of victims from January to May 2023.
