Malware-as-a-Service (MaaS) infections were the biggest threat to organizations in the second half of 2023, according to a new Darktrace report.
The 2023 End of Year Threat Report highlighted the cross-functional adaption of many of the malware strains. This includes malware loaders like remote access trojans (RATs) being combined with information-stealing malware.
Through reverse engineering and detection analysis, Darktrace researchers noted that “malware strains are progressively developed with a minimum of two functions and are interoperable with a greater number of existing tools.”
These malicious tools are particularly dangerous to organizations due to their ability to harvest data and credentials without exfiltrating files, making detection harder.
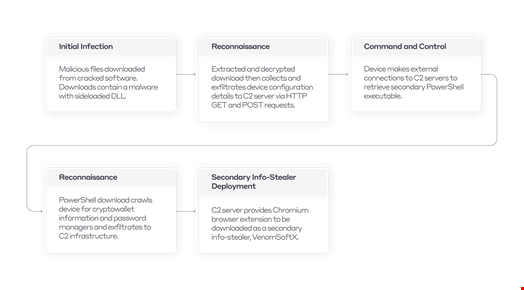
A prominent example of this was ViperSoftX, an information stealer and RAT malware known to gather privileged information such as cryptocurrency wallet addresses, and password information stored in browsers or password managers.
ViperSoftX was first observed in the wild in 2020, but new strains identified in 2022 and 2023 contain more sophisticated detection evasion techniques and capabilities.
Another example is the Black Basta ransomware, which also spreading the Qbot banking trojan for credential theft.
The most commonly observed MaaS tools in investigated threats during the period from July to December 2023 were:
- Malware loaders (77%)
- Cryptominers (52%)
- Botnets (39%)
- Information-stealing malware (36%)
- Proxy botnets (15%)
Further Shift Towards Ransomware-as-a-Service (RaaS)
The report also highlighted an uptick in RaaS attacks in 2023, marking a shift away from conventional ransomware.
It noted that the dismantling of the Hive ransomware group by law enforcement in January 2023 led to an increased proliferation of the ransomware marketplace. This included the rise of ScamClub, a malvertising actor that spreads fake virus alerts to notable news sites, and AsyncRAT, which has targeted US infrastructure employees in recent months.
Darktrace predicted that more ransomware actors will employ double and triple extortion tactics next year, utilizing the growing availability of multi-functional malware.
The firm said it expects the MaaS and RaaS ecosystems to continue their growth in 2024, further lowering the barrier to entry for cybercriminals.
Read here: LockBit Reigns Supreme in Soaring Ransomware Landscape
Attackers Using AI in Phishing Campaigns
Darktrace said it had observed threat actors employ other innovative approaches to bypass organizations’ defenses last year.
This included increasingly effective email attacks, such as phishing, which aimed to manipulate recipients into giving up sensitive information or downloading malicious payloads.
For example, 65% of phishing emails observed by Darktrace last year successfully bypassed Domain-based Message Authentication (DMARC) verification checks, while 58% of these messages passed through all existing security layers.
The researchers believe many attackers are leveraging generative AI tools to craft more convincing phishing campaigns and automate this activity.
Hanah Darley, Director of Threat Research, Darktrace, commented: "Throughout 2023, we observed significant development and evolution of malware and ransomware threats, as well as changing attacker tactics and techniques resulting from innovation in the tech industry at large, including the rise in generative AI.
“Against this backdrop, the breadth, scope, and complexity of threats facing organizations has grown significantly.”
