A tool which facilitates attacks on login frames has been responsible for a number of attacks.
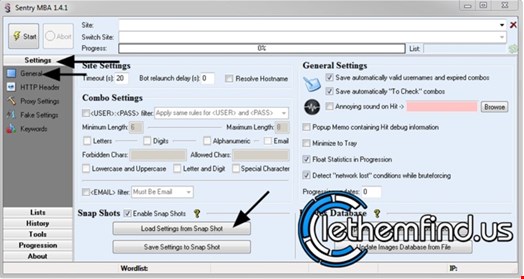
Speaking to Infosecurity, JUMPSEC managing director Sam Temple said that Sentry MBA works by harnessing proxies to conduct attacks. He explained that to use Sentry MBA effectively, the attacker needs to use a combination list of credentials and a configuration file that relates to the target.
“The tool is easy to use and draws information from three data sources to mount an effective attack: a configuration file to align the attack to a specific target; a “combo list” (list of valid usernames and passwords) and a list of proxies from which to relay the attack,” he said. “The real value is in the configuration files as it tells the tool how to attack a specific website; these are often traded on hacker forums for significant sums.”
Temple explained that while Sentry MBA is being traded on hacker forums, the real value is in combo and config lists, which contain user credentials for websites.
He said that if an attacker wanted to do a brute force attack, they could use a large combo list (500,000+ credentials), but would need to set up a config file and get the proxy to configure it for multiple tries to not get blocked. However, this is targeted at specific websites. “As you are not brute forcing using the same user account, you’re never going to lock an account,” he said. “The combo list credentials will be valid somewhere.”
Temple added that the config file will tell the tool how a website handles login requests, understand what captcha is running and know how many requests per proxy should be attempted. “When an attacker is using a good config file it can be almost impossible to distinguish the attacks from legitimate login requests. This makes Sentry very hard to detect, and defend against,” he said.
At the time of writing, the most popular config files were with login details for Netflix, Instagram and ‘Universal Email Access Checker’, with hundreds of downloads of each.
The tool was substantiated by SecureWorks researcher Rafe Pilling, who told Infosecurity that by using Sentry MBA attackers will not target specific websites, but will select a list of targets opportunistically. He explained that credentials are collected from Pastebin and credential dumps, and the config file is needed to know where to put credentials on a website and let you know if you’ve logged in successfully or not.
He said that the config file will show the tool where the username and password fields are, but he doubted that an average user could use or write a config file. “SentryMBA is like having a missile, but without the targeting information (the config) it wouldn’t be as useful,” he argued.
Pilling confirmed that the config files are sold online, and in one case were sold on 22 November for an attack on the National Lottery, although he was not certain that this tool was used in the breach.
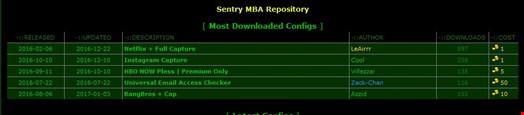
Asked how much Sentry MBA trades for, Pilling claimed that in the case of the sale for the National Lottery attack, the prices was listed as “250 gold”, although the value of that in $ will vary depending on how much “gold” you buy at once. However, this would be $2.50 or less based on the most expensive gold “coin” deal. “National Lottery was listed as 250 but not sure on currency, but expect would be a low amount of money, probably less than £100,” he said.
An explanatory guide, seen by Infosecurity, suggested that Sentry MBA can be used two ways: with or without configs. It suggested that as Sentry MBA is a very robust tool, it can crack a handful of different authentication types and it is pretty powerful at determining fakes or hits. This requires a lot of information to get started on a site.
“Sentry MBA if configured correctly, can determine when there is a fake response from the server - saving you time when cracking”, the guide said.
Looking at the guides presented online, Pilling said that it was fairly obvious that those involved in distributing it “were not well versed in opsec and give away too much”, and SecureWorks were able to identify one user easily.
He said: “We are not talking super skilled individuals, but tool which if you configure it and get data and [you have] got a process that works. It does not require a deep understanding of it as proxy IPs will tell you if it is working or not.”
Pilling said that the interface looks fully-featured and it appeared that someone had spent time creating it, and whoever created this knew how to present it, but this was not the sort of thing he encountered every day.
Asked how businesses can block this and prevent brute force attacks on authentication forms, Pilling said that brute force attacks are part of the weather of the internet; they happen and most organizations should have a way to prevent attacks on web authentication interfaces. He recommended a time penalty for multiple tries, and if there is a multiple password attempt on 50,000 accounts, have a method to detect a spike in authentication attempts, and block or watch out for multiple efforts coming from a proxy server.