Multi-cloud adoption is at an all-time high. While cybersecurity company Fortinet estimated in 2021 that 76% of organizations were using at least two cloud service providers (CSP), IT management provider Flexera found in 2022 that already 89% of enterprises had a multi-cloud strategy in line.
As a results, an increasing share of businesses’ digital assets are no longer in one place, either on-premises or in the cloud, but spread around multiple physical and virtual locations and run by several services providers.
Therefore, the traditional security strategies do not work anymore, Katy Anton, vice-president of security architecture at JPMorgan Chase, argued during a presentation at the Cloud & Cyber Security Expo, in London on March 8-9, 2023.
“In traditional cybersecurity strategies that we’ve been used to, everything is placed inside a castle. We have a strict perimeter where we can place our valuable assets and we’re looking to authorize trusted users to access this data,” she explained.
“In modern architecture, this way of doing is no longer relevant since our valuable data is spread around multiple third-party vendors. This forces us to adopt a zero trust approach, based on the least-privilege access principle and focused on securing identities rather than assets, with strong secret keys management, authentication and API security.”
Many organizations have transitioned to the multi-cloud approach without adapting their security strategy, Anton said.
She noted that Gartner has found that 90% or organizations will inappropriately expose their data in the cloud.
One of the critical reasons for that, she argued, is that many organizations wrongly assume that the CSPs fully ensure the security of the data they hand over to them.
“Gartner predicted that 99% of cyber incidents will be caused by misconfigurations from the customer by 2025. This is greatly due to a misunderstanding of the shared responsibility model,” Anton noted.
A Three-Tier Framework
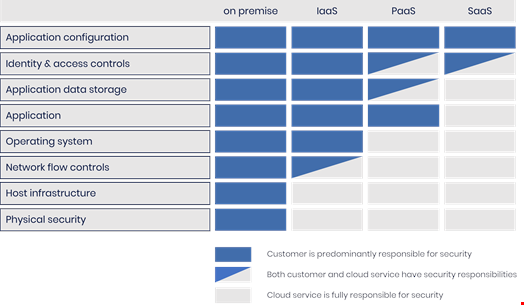
The shared responsibility model is a cloud security framework commonly used by CSPs like Amazon Web Services (AWS), Microsoft Azure and Google Cloud, explaining where their security responsibility ends, and where the customer’s responsibility begins.
The Cloud Standards Customer Council, an advocacy group for cloud users, describes three tiers of cloud service contracts – software-as-a-service (SaaS), platform-as-a-service (PaaS) infrastructure-as-a-service (IaaS) – and notes that users' responsibilities generally increase as they move from SaaS to PaaS to IaaS.
SaaS is a software delivery model where the vendor centrally hosts an application in the cloud that can be used by a subscriber. Dropbox, Zoom, Microsoft 365 or Google Workspace typically imply a SaaS contract. In this model, the provider is responsible for application security, as well as its maintenance and management.
PaaS consists in providing a platform, such as RedHat OpenShift or Google Kubernetes Engine for instance, that can be purchased and used to develop, run and manage applications. In this model, the vendor provides both the hardware and software and is responsible for security of the platform and its infrastructure.
IaaS is an infrastructure delivery model wherein a vendor provides a wide range of computing resources such as virtualized servers, storage and network equipment over the internet. AWS, Azure and GCP are the leaders of IaaS. In this model, the customer is typically responsible for maintaining security of anything they own or install on the cloud infrastructure (operating system, applications, containers, workloads, data, code…).
In all three models, however, some security responsibilities will always be the customer’s, such as identity and access management (IAM) of the assets, user security and credentials or endpoint security. Other security tasks will typically fall under the CSP’s remit, like the safety and security of the physical layer and all associated hardware and infrastructure, including the facilities that run cloud resources.
Sharing the Responsibility for Security Shortcomings
National Cyber Security Centre (NCSC) sets out a three-tier shared responsibility security model for cloud security, however this is simply a framework and not regulation.
Deryck Mitchelson, Check Point’s EMEA field CISO, spoke at the Cloud & Cyber Security Expo about how he helped the Scottish branch of the UK’s National Health Services (NHS) move to a native multi-cloud architecture.
He agreed with Anton that understanding the framework is critical in securely implanting a multi-cloud strategy.
Mitchelson told Infosecurity, “Many of our customers start their multi-cloud journey without fully understanding where their responsibilities are with regards to security.”
He added, “Organizations should go through their shared responsibility model with their CSP, look at guidance from government agencies and talk to their security provider, which can provide non-vendor insights, or even take care of some the heavy lifting away from them as well.”
The fault, however, is not only down to cloud users, Mitchelson said. “Cloud suppliers need to be much more transparent in what they do – and what they don’t do – and provide much more security by default.”
