A new phishing campaign targeting Mexican citizens with financial lures has been discovered by Cisco Talos.
Using Mexican tax-related lures, the spam emails distribute a new obfuscated information stealer that Cisco Talos called “TimbreStealer.”
In this new campaign, which has been active since November 2023, the threat actor directs users to a compromised website where the TimbreStealer payload is hosted and tricks them into executing the malicious application.
A Skilled Threat Actor Behind TimbreStealer
The current spam run was observed to mainly use Mexico's digital tax receipt standard called Comprobante Fiscal Digital por Internet (CDFI), according to the findings published on February 28, 2024
The phishing campaign uses geofencing techniques to target only users in Mexico, and any attempt to contact the payload sites from other locations will return a blank PDF file instead of the malicious file.
Talos researchers observed a sophisticated array of techniques in TimbreStealer’s code to circumvent detection, engage in stealthy execution and ensure its persistence within compromised systems.
These are contained in the malware’s embedded modules, which Talos researchers found to be structured in three layers.
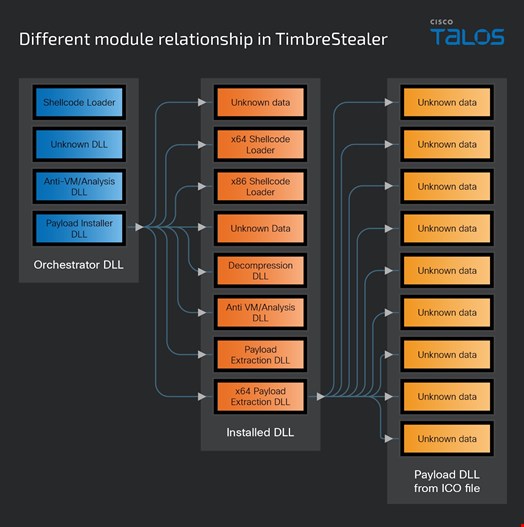
Some obfuscation techniques embedded into TimbreStealer “includes leveraging direct system calls to bypass conventional API monitoring, employing the Heaven’s Gate technique to execute 64-bit code within a 32-bit process, and utilizing custom loaders,” reads the report.
These features indicate a high level of sophistication, suggesting that the authors are skilled and have developed these components in-house.
Similarities with Mispadu Campaigns
Cisco Talos observed similar tactics, techniques and procedures (TTPs) in campaigns distributing a banking Trojan known as Mispadu.
In March 2023, Infosecurity reported on Mispadu being utilized in 20 different spam campaigns, which targeted victims in Chile, Mexico, Peru and Portugal.
Cisco Talos last observed Mispadu in September 2023.
“Although we could not find hard evidence linking the two campaigns, we assess with high confidence they are operated by the same threat actor, based on the same TTPs observed in this campaign and the previous activity distributing Mispadu, and the fact that once TimbreStealer started being distributed, we could not find any more evidence of Mispadu being used,” the researchers concluded.
