Infosecurity Opinions

Productivity and Security Don’t Have to Be a Trade-off
The modern workplace is awash with enterprise cloud apps, with employees and organizations alike increasingly seeking greater productivity – but this doesn’t have to mean a decline in security, says Eduard Meelhuysen

The Scope of the Mobile Banking Problem
Financial institutions present many opportunities for electronic theft, and cyber-attackers’ improved techniques and ever-more-aggressive malware makes them increasingly vulnerable, writes Jan Valcke

Cloud is the New Model for Innovation
Steve Schmidt discusses how the cloud is enabling security departments to embrace innovation and deliver new projects. He takes a look at the lengths cloud providers go to in order to ensure the highest levels of security for all customers, including those in traditionally security-conscious industries

What is the True Cost of a Data Breach?
Laurance Dine explains Verizon’s assessment model for gauging the financial impact of a security breach

Secure the DNS to Secure the Business
Securing DNS is crucial to mitigating APTs. Businesses that don’t are neglecting their best defense says Chris Marrison, consulting solutions architect at Infoblox

Security Requires a Blended, Collaborative Approach
Former FBI special agent, Thomas Trier, advocates the creation of a security task force within organizations

Five Anti-DDoS Tips for Hosting Providers
Rishi Agarwal explains how to beat DDoSers at their own game

Beyond EMV: Why Cloud-Based Payments Security is Key
Talk of EMV is dominating payments security news, but cloud-based solutions are critical for any business planning to make the switch. Chester Ritchie looks at how, when coupled with EMV, these solutions can ensure end-to-end protection in any environment and the highest level of transaction security

Balancing Agility with Security
Terry Greer-King discusses why businesses need to find a balancing act between business enablement and protection as part of a visibility-driven and threat-centric approach to security
Think You’re Safe from Malware? Think Again
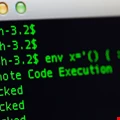
The bad guys no longer need to trick you into downloading malware onto your PC, says Jérôme Segura. They can do this without your knowledge by using exploits, meaning the tools you used to prepare against attacks are no longer sufficient

Keeping Ahead of New Hacker Techniques
In the effort to thwart cyber-criminals from stealing sensitive data, understanding how the enemy works is half the battle, says Rick Delgado

Threat Intelligence May Not Be The Answer
Dow Jones’s Rob Sloan queries whether the vendor drive for threat intelligence is really a key priority

Citibank’s Friction Reduction Patent: One Giant Leap for Online Banking
New patent from Citibank reduces the inconvenience of logging in for online banking users – it’s a big step, but there’s more to be done, writes Avi Turgeman

Point-Counterpoint: Should Companies Invest More in Skills or Tools?
Two experts assess what companies need to prioritize

People Are Not Broken, Passwords Are
For way too long our industry has been blaming the failings of an out-dated access mechanism on users and doing a good job of getting away with it, says Brian Spector

Decoupling Encryption: Building Bridges Between CISO and CTO
Data encryption is ever more important; indeed, it is demanded by regulators. As Certes Networks’ Paul German explains, it is only by decoupling encryption from its current ‘add-on’ role that the needs of both CTO and CISO can, finally, be addressed

Caught in the Middle? Minimising Network Migration Risks
Firms are increasingly falling foul of security holes and downtime as they struggle to shift applications onto the cloud and other modern platforms. Reuven Harrison, CTO of Tufin, believes careful network planning and security policy orchestration can ease their pains

Why PCI DSS 3.1 has Followed 3.0 so Quickly
PCI SSC has issued PCI DSS 3.1 outside its usual cycle in order to respond to threats. So what’s the emergency?

The Website Risk Assessment Tools Every Security Manager Must Use
The most basic step in dealing with attacks is finding a combination of assessment tools that can identify vulnerabilities and reduce exposure

25 Years On, Firewalls are Still Burning Bright
Firewalls have been the mainstay of network security for more than two decades and organizations still view the devices as a critical element of their defensive strategy





















