Infosecurity Opinions
Think You’re Safe from Malware? Think Again
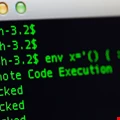
The bad guys no longer need to trick you into downloading malware onto your PC, says Jérôme Segura. They can do this without your knowledge by using exploits, meaning the tools you used to prepare against attacks are no longer sufficient

Keeping Ahead of New Hacker Techniques
In the effort to thwart cyber-criminals from stealing sensitive data, understanding how the enemy works is half the battle, says Rick Delgado

Threat Intelligence May Not Be The Answer
Dow Jones’s Rob Sloan queries whether the vendor drive for threat intelligence is really a key priority

Citibank’s Friction Reduction Patent: One Giant Leap for Online Banking
New patent from Citibank reduces the inconvenience of logging in for online banking users – it’s a big step, but there’s more to be done, writes Avi Turgeman

Point-Counterpoint: Should Companies Invest More in Skills or Tools?
Two experts assess what companies need to prioritize

People Are Not Broken, Passwords Are
For way too long our industry has been blaming the failings of an out-dated access mechanism on users and doing a good job of getting away with it, says Brian Spector

Decoupling Encryption: Building Bridges Between CISO and CTO
Data encryption is ever more important; indeed, it is demanded by regulators. As Certes Networks’ Paul German explains, it is only by decoupling encryption from its current ‘add-on’ role that the needs of both CTO and CISO can, finally, be addressed

Caught in the Middle? Minimising Network Migration Risks
Firms are increasingly falling foul of security holes and downtime as they struggle to shift applications onto the cloud and other modern platforms. Reuven Harrison, CTO of Tufin, believes careful network planning and security policy orchestration can ease their pains

Why PCI DSS 3.1 has Followed 3.0 so Quickly
PCI SSC has issued PCI DSS 3.1 outside its usual cycle in order to respond to threats. So what’s the emergency?

The Website Risk Assessment Tools Every Security Manager Must Use
The most basic step in dealing with attacks is finding a combination of assessment tools that can identify vulnerabilities and reduce exposure

25 Years On, Firewalls are Still Burning Bright
Firewalls have been the mainstay of network security for more than two decades and organizations still view the devices as a critical element of their defensive strategy

The Pitfalls of Common Key Generation Strategies
Strong encryption is essential, but the process of encrypting data is not that challenging, and nor is using the relevant tools, says Jonathan Carter

Cybercrime is Now Big Business
Cyber-attacks, no longer the actions of a few rogue individuals, are now big business. It’s a growth industry crying out for serious countermeasures

How Deniability is Covering Up Security Weaknesses
As businesses try to distance themselves from expensive public security failures, deniability is becoming the name of the game

Education is the Best Way to Protect Businesses
It is important to establish a foundation of security awareness and education among employees, writes Mike Duncan

Is Cloud Application Control the Silver Lining That Any Next Generation Web Security Solution Needs?
The ongoing consumerization of IT is creating a shadow IT community, of which CIOs have little or no control.

Safeguarding the Public Sector against the Threat of Device Loss
Recent data has revealed that two-fifths of those who work away from the office said their device had been lost or stolen in a public place , putting corporate and customer data at risk. The study also found that only around half of employees were aware that their organization had a remote working policy in place, with a quarter admitting they have broken it.

Are you Immune to the Venom Security Flaw?
The Venom security flaw has been described by some as bigger than Heartbleed, the vulnerability in OpenSSL which allowed adversaries to eavesdrop on internet communications, steal data and impersonate services and users. Elias Manousos assesses this claim

Transforming Cybersecurity into a C-Suite Priority
For many IT professionals, attempting to promote the urgency of security preparedness to senior leadership feels a bit like screaming in a soundproof booth

Why Outdated Fraud Detection is Costing Companies Customers
Why are retailers driving customers away in their bid to secure sensitive data? Online fraud prevention specialist, Tony Larks, investigates the flaws in today’s authentication solutions and sets out a new path for protecting valuable customer relationships




















