Infosecurity Opinions


Detect Active Compromises to Boost Cybersecurity
Your IDR program must include a formal chain of command for response and crisis communications.

Code Signing in the Age of Cloud and IoT
Code signing is the key to unlocking the IoT’s true potential, ensuring security and safety are embedded in every device.

Top Thoughts for GDPR Third-Party Management
While you are working diligently to help ensure your own organization is compliant with GDPR, your organization is explicitly responsible for the readiness and conduct of the third parties that store or process your EU citizen’s personal information.

Automation is Not Enough to Solve the Cybersecurity Skills Gap
The blending of humans and automation is going to become increasingly necessary in the world of cybersecurity,

Simple Social Login for Users and Attackers
Social login providers could dramatically improve security for themselves and site operators by applying for social logins the same security and validation tools they apply on their own login pages and account creations.

Post Equifax Plea: Change Your Software Security Practices or Be Damned (Again)
Anyone looking to identify a fixable vulnerability or single out a culprit inside of Equifax to explain this breach is missing the bigger picture.

Why Identity Protection in the Cloud Matters
With so many applications operating in the cloud, it is getting harder for companies to know what data is transmitted, who is accessing it, and where it goes.

Data Breaches Often Originate Behind Your Defenses
Time has shown us the majority of data breaches originate inside company walls.

Chain Phishing Attack Against Office 365
A successful phishing lure, targeting an O365 user, will start a series of events via a chain methodology.

Three Mistakes in Responding to Security Incidents, and What To Do Instead
Organizations continue to make the same three potentially costly mistakes that could be costing them millions in lost business, tarnished reputation, and even lawsuits.

Securing Communications Networks Against Quantum Attacks
Stored, encrypted data could someday become vulnerable to quantum computer decryption attacks.

What Security Should Mean to Today's CIO's
CIOs are struggling to keep pace with their current business functions, which can often leave them feeling “flat-footed” when it comes to being proactive about security.
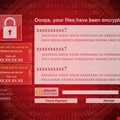
Why Wannacry Was Just a "Warm-Up"
It is only a matter of time before Western economies such as the US and the UK are hit by a massive cyber-attack aimed at taking down critical utilities or financial infrastructure.

The Perfect Way to Say Goodbye
Farewell to information security staff members can be smooth if you follow the best practises.

Understanding The Physical Damage Of Cyber Attacks
Everyone must be prepared to prevent cyber-attacks that's meant to cause physical damage too.

Simplify NIST Cybersecurity Framework Adoption
How to simplify NIST Cybersecurity Framework adoption and gain the cyber resilience benefits.

A Holistic Approach to Security Compliance
Many of the compliance standards have similar nuts and bolts, but are composed with slightly different wording.

Malware's Journey Through the Cloud
Malware is only going to become more advanced and look to cause more damage to enterprises and corporate data as it moves to the cloud.

How Big is Your DDoS Mitigation Gap?
The DDoS mitigation industry is scaling up capacity following a consistent increase in the number of DDoS attacks.






















