Infosecurity Opinions

Three Mistakes in Responding to Security Incidents, and What To Do Instead
Organizations continue to make the same three potentially costly mistakes that could be costing them millions in lost business, tarnished reputation, and even lawsuits.

Securing Communications Networks Against Quantum Attacks
Stored, encrypted data could someday become vulnerable to quantum computer decryption attacks.

What Security Should Mean to Today's CIO's
CIOs are struggling to keep pace with their current business functions, which can often leave them feeling “flat-footed” when it comes to being proactive about security.
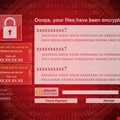
Why Wannacry Was Just a "Warm-Up"
It is only a matter of time before Western economies such as the US and the UK are hit by a massive cyber-attack aimed at taking down critical utilities or financial infrastructure.

The Perfect Way to Say Goodbye
Farewell to information security staff members can be smooth if you follow the best practises.

Understanding The Physical Damage Of Cyber Attacks
Everyone must be prepared to prevent cyber-attacks that's meant to cause physical damage too.

Simplify NIST Cybersecurity Framework Adoption
How to simplify NIST Cybersecurity Framework adoption and gain the cyber resilience benefits.

A Holistic Approach to Security Compliance
Many of the compliance standards have similar nuts and bolts, but are composed with slightly different wording.

Malware's Journey Through the Cloud
Malware is only going to become more advanced and look to cause more damage to enterprises and corporate data as it moves to the cloud.

How Big is Your DDoS Mitigation Gap?
The DDoS mitigation industry is scaling up capacity following a consistent increase in the number of DDoS attacks.

Total Recall - Better Security for Your Network
Without a level of historical insight, it is impossible to build a complete security posture.

The Weakest Link in Cybersecurity
Email technology may well save the reputations of countless organizations and individuals.

A Surgical Approach to Software Security: Protecting Software from the Inside Out
We must focus on a preemptive diagnosis and cure designed to eliminate the opportunity for problems both today and in the future.

Big Questions to Ask About Security in the Cloud
A guide to use when discussing application infrastructure and operations with cloud providers.

Data-Centric Security: Protecting What Really Matters
Data-centric, rather than network-centric, security strategies are becoming the norm in our new digital environment.

Why 2017's Phishing Attacks Teach Us All to Beware
If these attacks tell us one thing, it’s this: don’t be fooled into thinking attacks only happen to others.

How Can Data Forensics Help The Fight Against Malware?
IT teams need better intelligence, that insight can come from remediation in the form of network forensics.

Changing Cyber Threats Call For New Protection Strategies
Changes in cybercrime techniques mean that companies need to be sure their strategies—from security practices to cyber insurance coverage—keep pace.

You Wouldn't Re-Use a Needle, So Why Re-Use a Computer?
We visit websites, open email attachments, download documents, and plug in USB devices – all on the same device – seemingly oblivious to the potential threat of infection without even washing our virtual hands.

Smart Buildings Require Full-Stack Cybersecurity
Smart buildings combine operational technology (OT), information technology (IT) and IoT devices.




















