Infosecurity Opinions

Keep an Open Mind on Open Ports
The time has come for IT to think like that persistent outsider and increase their understanding of their vulnerabilities first.

API Hooking - Evading Traditional Detection with Stealthy New Techniques
API hooking is one of the memory-resident techniques cyber-criminals are increasingly using.

Organizations Must Adapt to Evolving DDoS Attacks
At the source of a DDoS attack, it can be difficult to differentiate between someone uploading a file and someone perpetrating an attack.
The Automat(i)ons are Coming!
Businesses need to start to use the data it holds within the business, to protect the business.

Why Machine Learning will Boost Cyber Security Defenses amid Talent Shortfall
Machine learning is our best hope for securing the exponential growth of technology. Imagine systems designed to learn the behavior of its users.

Can Cloud Storage save you from Ransomware Attacks?
If cloud storage is the way to go, how does it handle attacks, and should you back up your data in the cloud all of the time.

Protecting Your Company's Assets: How People and Machine Both Play Vital Roles
Today, machines are infinitely more intelligent – capable now of much more than simply augmenting, then eclipsing physical capability.

How IoT Device Discovery and Activity Detection can Work
IoT device discovery offers a critical foundation to an IoT security solution.

Look at the Past to Fight Today's Attacks
Even with stringent controls and up-to-date security software, malicious actors are adept at breaking through barriers.

Why Trust Keeps the Connected World Ticking
The Importance of Good Code Signing - Why Trust Keeps The Connected World Ticking.

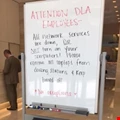
Creating the Right Perception for Security Awareness Training
“Just-in-time” security training can certainly help the individual, but what message is being sent to that employee?
Fighting Cyber Threats with an Open Data Model
Behavioral-based analytics, machine learning and more flexible analytic solutions are required to defend the enterprise.

Cyber Warfare: How Militaries Defend Themselves Online
As hackers make use of increasingly destructive cyber weapons, how are militaries fortifying their digital defenses?

Bull-Mastiff or Toy Poodle: What's Guarding your Front Door?
Authentication is one of the first lines of defense for protecting your company’s assets, but not all authentication schemes are equally capable of withstanding assault.

Evolving Access to Applications
Today’s digital ecosystem demands an altogether more rapid, seamless and open approach to access.

The Questions Before you Buy and Use IAM Technology
An IAM program requires buy-in from the enterprise and all the stakeholders, and this is required from people and budget across the enterprise.

Could your Medical Device Catch a Cold?
Implanted devices have been around for decades to allow doctors to collect vital patient data, but many of these devices were distributed without any type of encryption or defensive mechanisms in place.

How to turn Cybersecurity into a Business Asset
World-class organizations recognize that cybersecurity can, and should, be a powerful enabler for business.
Legal Ramifications of a Ransomware Attack
One of the most striking items of Petya/NotPetya was a major international law firm having to announce that they had been affected by the outbreak.

Data Privacy Best Practices for Employees and Employers
Employees and HR departments need to be vigilant with the data they are sharing and receiving.






















